On March 30, 2026, compromised versions of Axios npm packages were released that would automatically install a Remote Access Trojan. The window of distribution was between Monday, March 30, 2026 at 7:59 PM EDT and Tuesday, March 31, 2026 at 12:26 AM EDT. As far as we know, none of the Hubs Foundation GitHub repositories were affected themselves and most of them have no direct dependency on Axios; however, the turkey-portal repository does depend on Axios and could have potentially downloaded the compromised packages to your computer during the window of distribution if you ran npm install. It also can’t be ruled out that one of the dependencies of our dependencies (or one of their dependencies, and so on) doesn’t depend on Axios and so could have triggered the download of a compromised version to your computer (or you could have picked it up somewhere else too).
How to check if you’ve been compromised:
Search your system for a folder named plain-crypto-js:
If you have more than one drive, you’ll need to run these commands on all of the ones that could have Node packages on them.
Windows (in a Command Prompt. Type Command Prompt in the Windows Search bar, select Open.):
dir C:\*plain-crypto-js /AD /S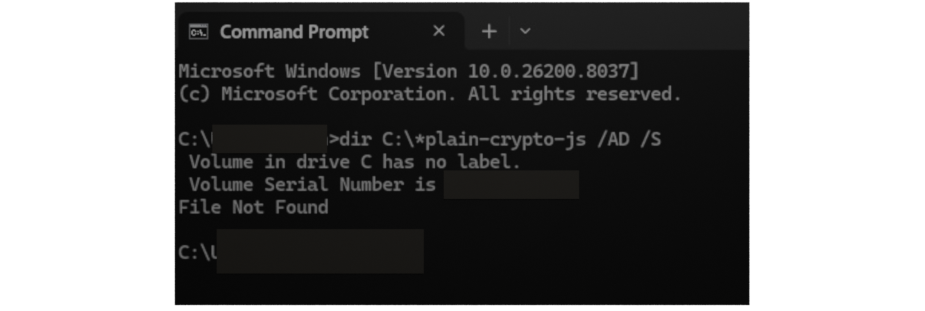
macOS & Linux:
find ~ -type d -name "plain-crypto-js" -path "*/node_modules/*" 2>/dev/nullCheck the npm global packages:
Windows (in a Command Prompt):
npm list -g axios 2>nul | findstr "1\.14\.1|0\.30\.4"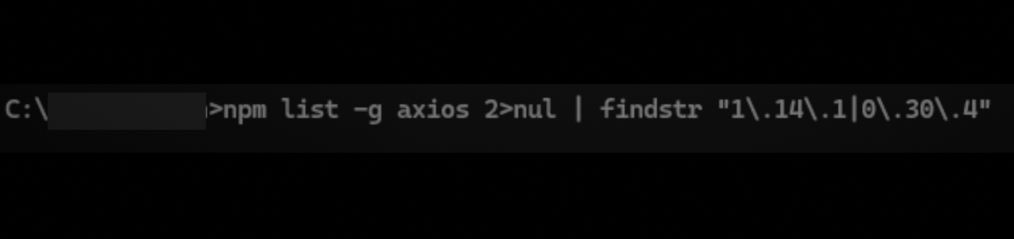
macOS & Linux:
npm list -g axios 2>/dev/null | grep -E "1\.14\.1|0\.30\.4Check for the Remote Access Trojan:
Windows (in a Command Prompt):
dir "%PROGRAMDATA%\wt.exe" 2>nul && echo COMPROMISED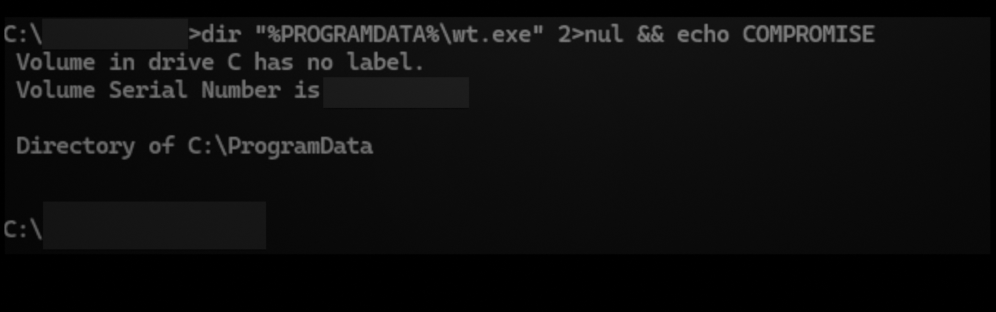
macOS:
ls -la /Library/Caches/com.apple.act.mond 2>/dev/null && echo "COMPROMISED"Linux:
ls -la /tmp/ld.py 2>/dev/null && echo "COMPROMISED"If any of these commands return something, you are likely compromised.
You should also check to see if you built any Docker containers during the window of distribution that could have downloaded a compromised package. You can do that with the following command:
docker images -a --format "table {{.Repository}}\t{{.Tag}}\t{{.ID}}\t{{.Size}}\t{{.CreatedAt}}\t{{.Repository}}:{{.Tag}}"And you should check your GitHub repos to see if any actions were run (either manually or automatically) during the window of distribution. If any were, then you should check the logs to see if there is any sign that a compromised version of the Axios package was installed (check the link in the more information section for what to do).
What to do if you’ve been compromised:
For more information on this attack:
Got problems? Visit us in our Discord dev-general channel.
